Streamlining Electronic Security Projects
Navigating complex security projects
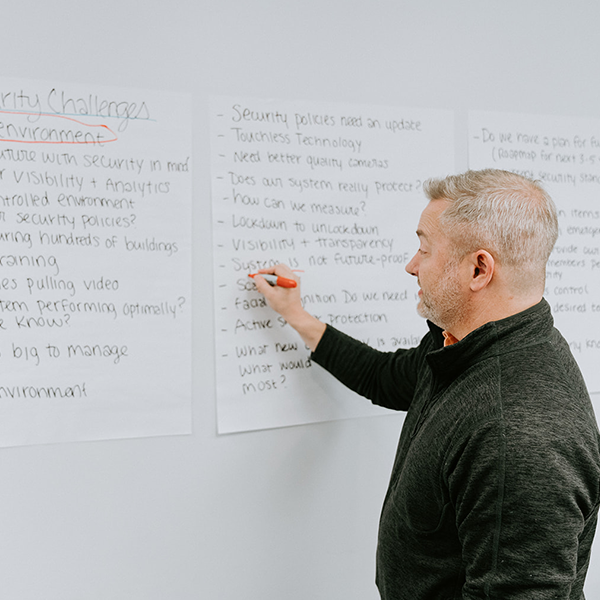
Designing and implementing critical security infrastructure can be complex and frustrating. No two electronic security systems are alike, making it challenging to anticipate and prepare adequately for upcoming security initiatives.
Serving as your strategic ally, we commit to guiding you through a clear and consistent process, ensuring ease of comprehension and a steadfast partnership in navigating the intricacies of your security project.
After years of working with organizations of all shapes and sizes, we’ve identified a strategic framework that delivers consistent and predictable results.
Proven Security Solutions Framework
More than an integrator
We believe that deep partnerships produce the best results. Our clients believe it, too.
Our clients include


Ready to get started?
Creating complex security systems can be tedious, confusing, and overwhelming.
Our team of industry experts can work with your team to help achieve any security objectives through a predictable and transparent process.
Reimagine electronic security with 3Sixty Integrated.